How to install Enigmail
Pre-requisites
Enigmail uses GnuPG (also called GPG), so make sure GPG is installed.
Then, make sure your mailer and OS are supported by Enigmail. At the time I write this article, there is no package compiled for Solaris x86.
The rest of this article applies to Enigmail with Thunderbird.
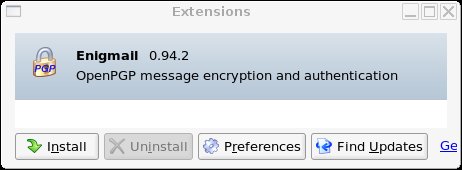
Installing Enigmail
Download Enigmail. For Thunderbird, it's a (extension .xpi). Use a right-click to download it (if you click on it with Firefox, you'll install the plugin in Firefox which is quite useless !).
- Then, install the plugin in Thunderbird: Tools -> Extensions -> Install
- Restart Thunderbird
Recommended configuration
Enigmail is configured directly from within Thunderbird. There are two menus to check out:
- OpenPGP -> Preferences:
- Basic settings: check or set GPG's executable path. If you don't have a clue where it is:
- On Linux, locate gpg (whereis gpg, which gpg, locate gpg...). Typically, it'll be in /usr/bin.
- On Windows, search for gpg.exe. Typically, something like c:\program files\gnupg\gpg.exe
- If you only see the Basic tab, but no other, check the "expert" mode in the Basic tab.
- Sending: enable
- "Encrypt to self" (makes sure that you'll be able to re-read encrypted emails you've sent to your recipients !),
- "Always trust user ID",
- "Always confirm before sending" (I like to make sure I'm sending confidential stuff to the right person !),
- "Rewrap signed HTML before sending",
- "allow empty subject" (just to avoid the warning when subject is empty)
- Key selection: display selection when necessary (only shows the key selection window when it does not know which key to choose)
- Advanced: encrypt if replying to encrypted message (seems a good thing)
- Basic settings: check or set GPG's executable path. If you don't have a clue where it is:
- Edit -> Account Settings -> OpenPGP Security
- Enable OpenPGP support (enigmail) for this identity
- Use email address of this identity to identify OpenPGP key.
Using Enigmail
Generating your own key pair
You need a key pair to send/receive encrypted/signed emails.
Thunderbird -> OpenPGP -> Key Management -> Generate -> New Key Pair

For example:
- Choose expires in 5 years (I do not recommend "does not expire")
- Choose your passphrase. A passphrase is a long password, a sentence. Choose something you can type easily, but don't choose anything too short: your key pair might get compromised, and then the attack can sign under your Id, decrypt your emails etc.
- You can use default settings for other parameters, though I prefer using an RSA key than DSA (in the Advanced panel)
Importing an archived key pair
There are several ways to do that:
- read an email containing your key pair, right click on the key pair and import it in your keyring.
- or OpenPGP -> Key Management -> File -> Import keys from file, and select your archived key pair.
- or OpenPGP -> Sender's key -> Import public key (this will import the public key only)
- or copy your public and secret key ring in GnuPG's directory (e.g. ~/.gnupg)
Sending your public key to others
The easy way
From Thunderbird, write a new message. Click on the message's OpenPGP menu: "attach my public key". That's all.The complicated way: exporting your public key
Now, if you insist on doing it the hard way ;-):- Thunderbird -> OpenPGP -> Key Management

- Select your own key
- Then File -> Export Keys to File.

- When it asks "Do you want to include your secret key..." of course, you answer No (IMPORTANT !).
- Then, include the resulting file in your mail (or wherever you want it). Your public key is not secret, you do not need to password-protect it.
Importing recipients' keys in your keyring
The easy way
- Right click on the attached key in the mail -> Import OpenPGP key
The hard way
- Thunderbird -> OpenPGP -> Key Management -> File -> Import keys from file
- Select the file containing the keys to import
Sending an encrypted email
Very easy:
- Write a message (as usual)
- Click on the small key on the bottom right corner of the message window
- Send the message, that's it !

Depending on your configuration, another window may be displayed asking you confirm/select your recipient's key. This also happens if Enigmail can't find the right key to use for your recipient. If the key isn't in your keyring, import it. Sometimes it's already there, but not for the right email: you can still use that key. A key is attached to an end-user , not to an email. Email is just a common way of naming a key.
Sending a signed email
Well, it's similar to sending an encrypted email, but instead of selecting the small little key, select the small pencil.
Now, guess what ? An advanced topic: how to send an encrypted and signed email ? Well check both pencil and key !
For users with several emails
You may use a different key pair for each e-mail, or the same key pair for several emails. As you wish.
If you use a different key pair, you'll have to memorize several passphrases and store several key pairs. Beware that all your key pairs are treated independantly. You cannot decrypt a document for your key pair A with your key pair B. And when you decrypt with key pair A, obviously you must provide A's passphrase (not B !). This solution is usually more complicated, but it may be useful for example if you wish to completely separate your professional emails from your personal ones.
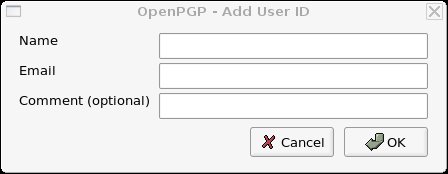
In other situations, it's interesting to attach several emails to the same key pair. For example, Pico with emails pico@crocodile.comThis email address is being protected from spam bots, you need Javascript enabled to view it and pico@crocodile.frThis email address is being protected from spam bots, you need Javascript enabled to view it wants to attach both emails to his key pair Pico. To do so, you have to
- Thunderbird -> OpenPGP -> Key management
- Select your key pair
- Manage User IDs

- Hit the add button
- Enter your new identification. Here Pico would probably enter “Pico" as name, " pico@crocodile.frThis email address is being protected from spam bots, you need Javascript enabled to view it and "Great crocodile" as comment.
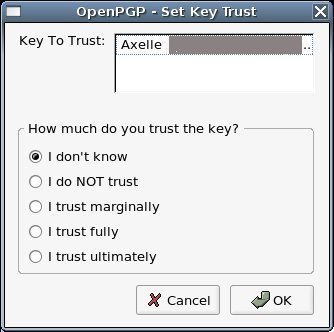
How to ged rid of that "untrusted good signature" message
Before importing a key into your keyring, it's important to check the key really owns to the person you think it does. How far you want to go in your verifications is really up to you. They may be nearly implicit (that friend has told you he'd send you a key and you received it a moment later - you estimate the risk an attacker impersonates your friend is really unlikely) or much more thorough (calling the person, checking his credentials etc).
GPG takes into account the amount of trust you have in a given key. If you have made real checks, you can fully trust the key. If you have made little verifications but that's enough for you, you may also fully trust the key. On the contrary, if you received the key by an unknown channel you do not highly trust, you can tell GPG.
By default, in GPG, the only key you ultimately trust is yours (logical, huh ?). All others are untrusted. This is why you get a message telling you a given signature is good (it is valid) but untrusted. To get rid of that message, you've got to carry out necessary checks about that key, and then set its trust level to ultimate.
Once checks have been done, you set trust level as follows:
- OpenPGP -> Key management
- Select the key, right click
- Set Key Trust: choose the appriopriate level. Choose ultimate to get rid of the warning.
Security basics: all you need to know
What's a key pair ?
A key pair is made of a private key (private meaning "secret" - do not send this to anybody) and a public key (this one is not confidential). Both keys are related, so that when an operation is done with the private key, you need the public one to reverse the operation, and reciprocally if you use the public key, you need the private one to revert.
What's a key ring ?
A keyring is a key... ring ;-) That's the location where you store all your public and private keys, including public keys of other persons.
GnuPG uses 2 different keyrings:
- a public key ring (default name : pubring.gpg), where you store your own public keys and others.
- a private key ring (default name: secring.gpg) containing your private keys. This keyring should be kept secure.
Encryption and confidentiality
Encrypting a document is about its confidentiality.
Suppose I want to send a document to my husband, but I don't want Pico to be able to read it (I'm bored with security examples with Alice and Bob ;-). So I encrypt it in a way that only my husband can read it. Now, just think two seconds how to do that... it's easy: I encrypt it with my husband's public key. Indeed, my husband keeps his private key safely, Pico does not have that key. So my husband will be able to decrypt the document but not Pico !
A common mistake is to encrypt a document with your own public key. Actually, this is really silly, because you're the only one to be able to decrypt the document. Your recipient does not have your private key !
Signing and authenticity
Signing a document has a different use: it's about document's authenticity.
Now imagine I want to send a nice recipe to my husband. How can he be sure this recipe is authentic and hasn't been modified (with arsenic ?!) by Pico ? To guarantee this, I sign the recipe with my private key. If I am able to use my private key successfully, it means I really signed (i.e approved) the document. When my husband gets the document, he verifies my signature using my public key. If that works, he's guaranteed the document was signed by someone owning my private key... if I keep my private key secret, he's guaranteed this is really me.
Certificates
You can skip this if you're out of time.
Now, actually, if you really have a close look to my last scenario, there's something nasty Pico could do. How does my husband retrieve my public key ? Can he really be sure it's mine ? Just imagine Pico sends him a fake email with his own public key instead, signs a bad recipe with his private key and sends the signed recipe (using another fake email) to my husband... My husband's going to verify a valid signature and he'll think it comes from me... though it's only really an authentic recipe of Pico's !
To counter this problem, people commonly use certificates. A certificate can basically certify anything, but here we're interested in certifying public keys. A certificate certifies that my public key (for e.g id=01298) really belongs to me (and not Pico). This is usually certified by a third party (hoping that third party asks for the adequate proof of my identity). I'm not getting into details here as to how certificates are generated and how they are verified, but it's just to let you know that they do exist and are really useful...
FAQ
- Can I recover my public key from my private key ? No, this is not possible.
- What's the relation between emails and keys ? Key pairs are associated to end-users. Emails are a common way to name a key. They help identify a given key pair.
- Why must I keep my secret keyring secure ? Because its protection isn't said to be very efficient.
